
What is Risk Assessment? How many steps are involved? Why is it important for businesses?
Risk Assessment is a process that covers everything from identifying risks and analyzing them to evaluating the impact of those risks.
InterRisk Asia offers the latest workplace safety tips and risk management insights

Risk Assessment is a process that covers everything from identifying risks and analyzing them to evaluating the impact of those risks.

What is BCMS? Why Is It Important? Keep your business resilient through unexpected events Nowadays,

In today’s world, businesses face many unpredictable challenges such as natural disasters, cyberattacks, and even
In our previous article, we explored strategies for selecting appropriate business continuity strategies for organizations

Today’s business world faces constant threats—from natural disasters and cyberattacks to supply chain disruptions. These

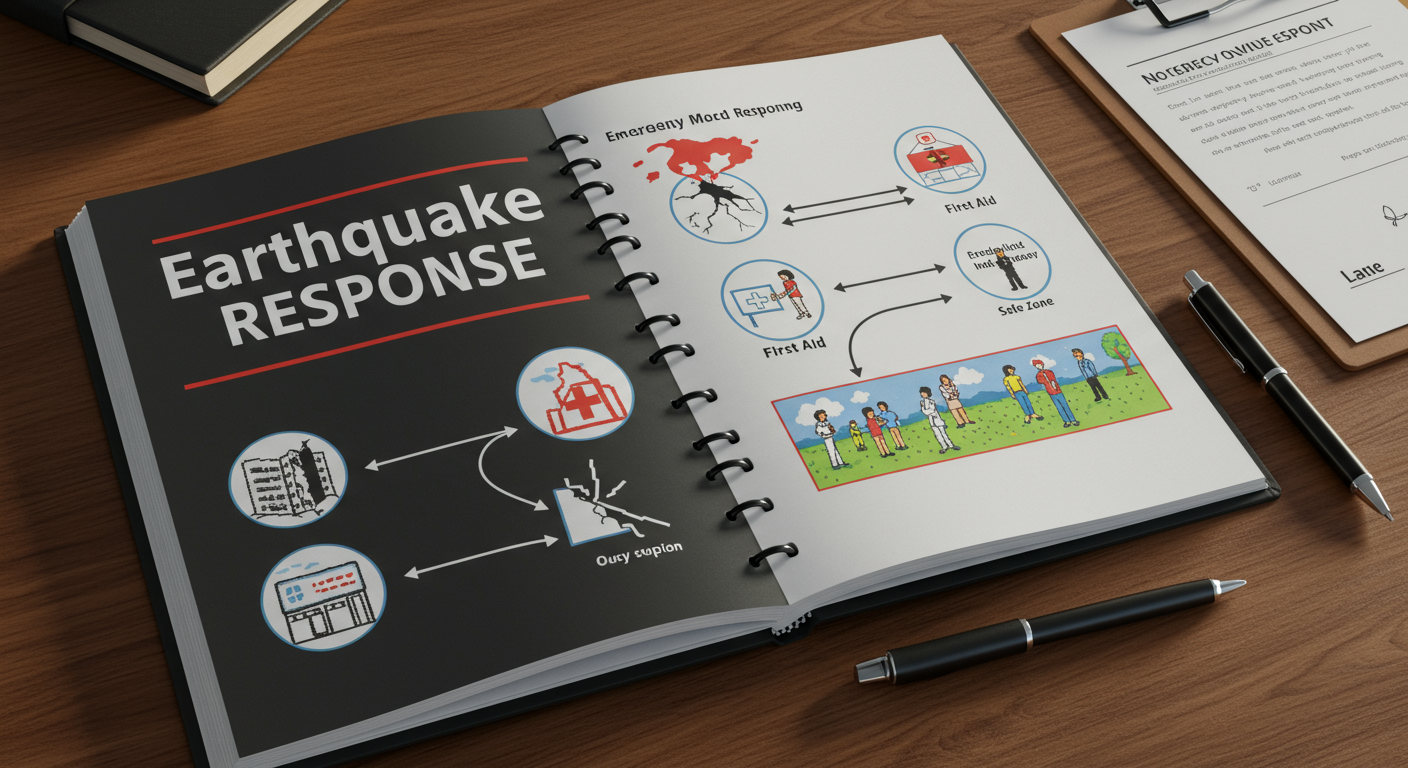
On Friday, March 28th 2025, an earthquake in Myanmar sent tremors across parts of Thailand.

This week, let’s look at another real-world example of infrastructure failure that highlights the importance

How to Perform a Business Impact Analysis (BIA) for Your Organization In a world where

Why BIA is the Key to an Effective BCMS In today’s world, businesses face a
Talk to InterRisk and take the first step toward a safer, risk-free business